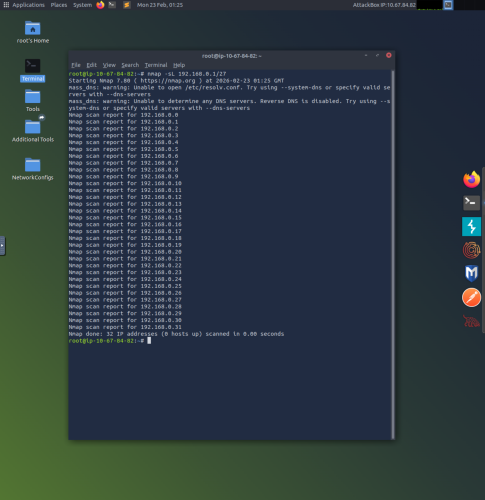
1. This example uses the “nmap -sL 192.168.0.1/27” command to do a list scan (-sL) of the 192.168.0.1 IP address and its 27 subnet and returns with 32 IP addresses.
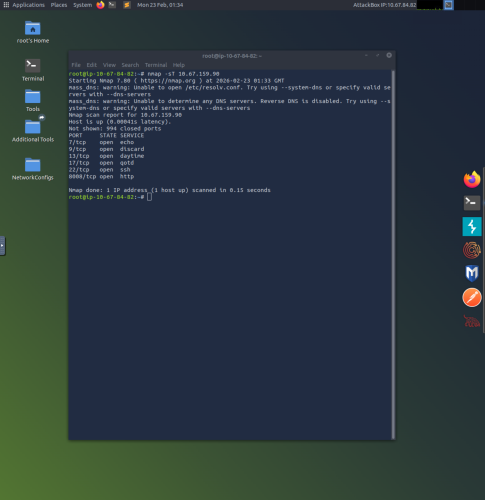
2. This example uses the command “nmap -sT 10.67.159.90” to do a TCP connect scan (-sT) on the 10.67.159.90 target IP, where it finds 6 open TCP ports (7,9,13,17,22, and 8008).
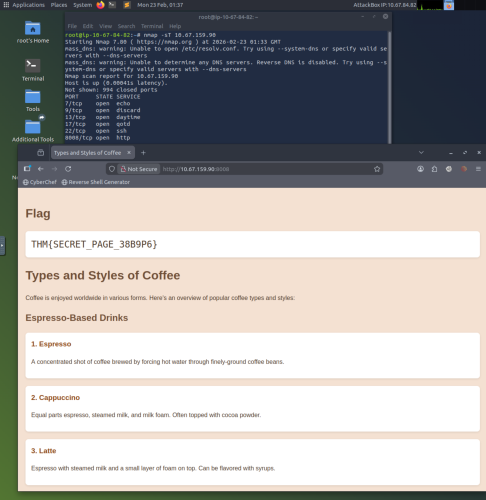
3. This example uses Firefox to check the open http port at 10.67.159.90:8008 to reveal the website contents with the desired flag code.
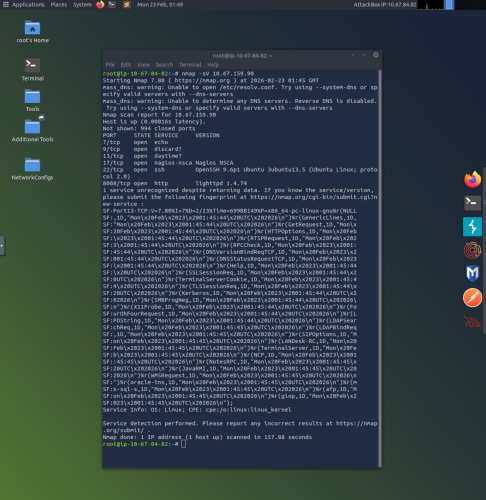
4. The final command used is the “nmap -sV 10.67.159.90” which probes open ports to determine service and version information (-sV). This reveals that on port 22 (SSH) the target machine is running OpenSSH 9.6p1 on Ubuntu 3ubuntu13.5 using Ubuntu Linux; protocol 2.0, and displays other open port information.
